It’s relatively easy using current technology to set up your own blog or website, and if you use an online hosting platform then typically they will take care of issues like scaling and denial of service attacks for you, although they may well charge you for the privilege. If on the other hand you set up a virtual machine on a generic cloud platform (such as Digital Ocean or AWS) and run your own company website or blog using something line WordPress, then you may find you’re exposed to issues that from time to time may render your site inoperable.
The problem: if it’s just “you” with a single IP address and a single instance of your website, it’s relatively easy for the site to become overwhelmed by a potential attacker or abuser.
One solution: put someone / something big between you and any potential aggressor, our example in this instance is a company called CloudFlare.
How does it work
Cloudflare effectively provides what is termed a reverse proxy service, whereby they accept all requests on behalf of your website and forward what they consider to be valid request to the real website, and discard what they consider to be attacks or abuse. Sounds relatively trivial, but there is a lot going on here under the hood.
In order to make this work, you need to let CloudFlare serve up your DNS records for you, so rather than setting up your DNS with your domain provider, you need to point your domain provider at Cloudflare, and use Cloudflare’s online control panel to manage your domain records. Not terribly difficult, but you do need to trust Cloudflare to manage your domain, and you do need to give up your current DNS management in favour of a new control panel, fortunately the Cloudflare panel is pretty good.
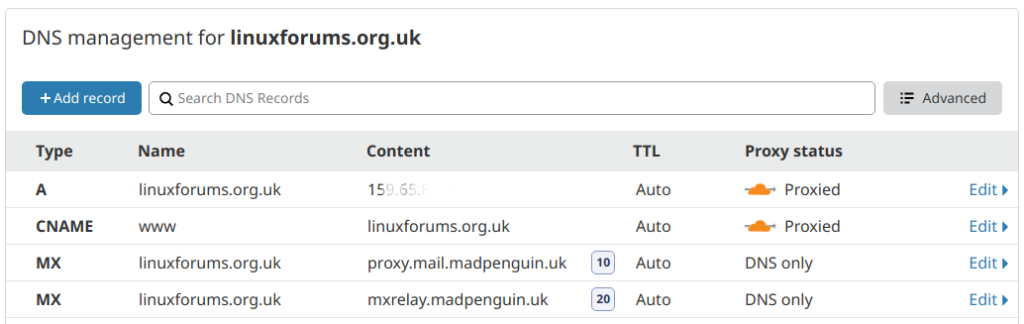
Once you’ve done this, you will find that when you try to lookup the address of your website using nslookup or an online checking tool, instead of seeing the address for your website, you will actually see an address (actually a few addresses) that reference Cloudflare. So anyone who tries to visit your website is actually visiting Cloudflare, although what they will see (assuming they’re not an attacker) is the content you published. By default visitors will see a CloudFlare SSL certificate, although there are paid-for options if this is a problem for you.

And that’s pretty much it, you’ve now made friends with and are sitting next to the captain of the school Rugby team and to get to you, they’re going to have to come through him.
Additional benefits
Unless you are what would be classed as a high volume site, then this might not be of any interest, but this specific service provides a caching facility such that any parts of your site that don’t change, are typically served up via the CloudFlare cache, rather than being served up by your website. Bottom line, your website has to do less work and uses less bandwidth, and visitors get images etc delivered by a much faster server (i.e. the cache) which is closer to them. So your pages will effectively be delivered faster with less latency for the visitor.

Analytics
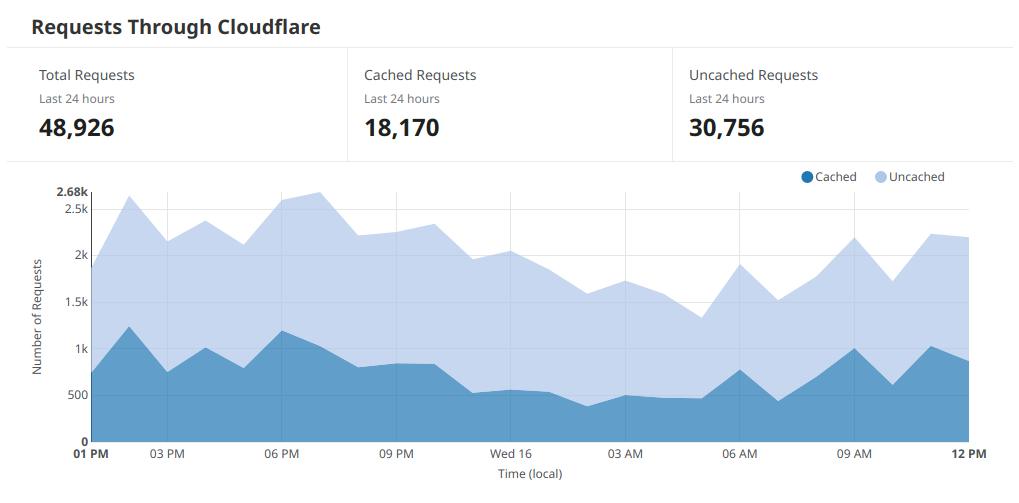
Whereas you will probably have an analytics packages installed for your site, something like Google Analytics or WordPress Jetpack, typically these will produce reports that centre around page views. From a server perspective it’s often useful to know how much actual work the server is doing, and indeed how much work your reverse proxy is saving, which is something the Analytics console provides.
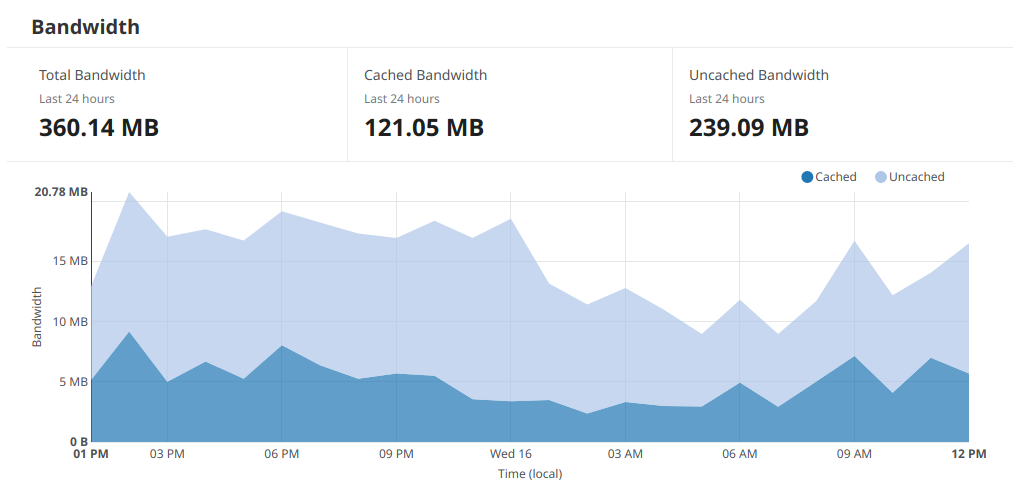
And if you’re hosting provider is charging you for bandwidth, or more likely you have a bandwidth threshold above which you are charged, then it’s quite handy to see how much traffic is actually being used, not only to know what your charges might be before they land on the doorstep, but also to make sure they’re what they should be (!)
All in all this sort of service is becoming an essential tool if you’re hosting your own website and don’t want to avoid calls along the lines of “did you know your website is really slow” or “did you know your website is down”.
If you have any experience with alternative solutions, please leave us a comment!